Our engineers have discovered a Use-After-Free vulnerability in libpng (CVE-2026-33416)!
One of our engineers recently discovered a vulnerability in the image processing library libpng, and a security advisory has been published.
The summary of this vulnerability is as follows:
Summary of the libpng Vulnerability (CVE-2026-33416)
Advisory: GHSA-m4pc-p4q3-4c7j
CVE: CVE-2026-33416
CVSSv3: 7.5
CWE: CWE-416(User-After-Free)
Impact: High
Scope of Impact: libpng 1.2.1 ~ 1.6.55
Attack Vector: Vulnerable to remote attacks (e.g., by uploading a malicious PNG image)
This vulnerability is classified as a “Use-After-Free” vulnerability; processing a specially crafted PNG image could lead to information disclosure or arbitrary code execution.
libpng is a widely used library employed in software around the world, and this vulnerability could affect many systems.
A visual representation of the attack
An attacker can carry out an attack by tricking the victim into uploading a malicious PNG image.
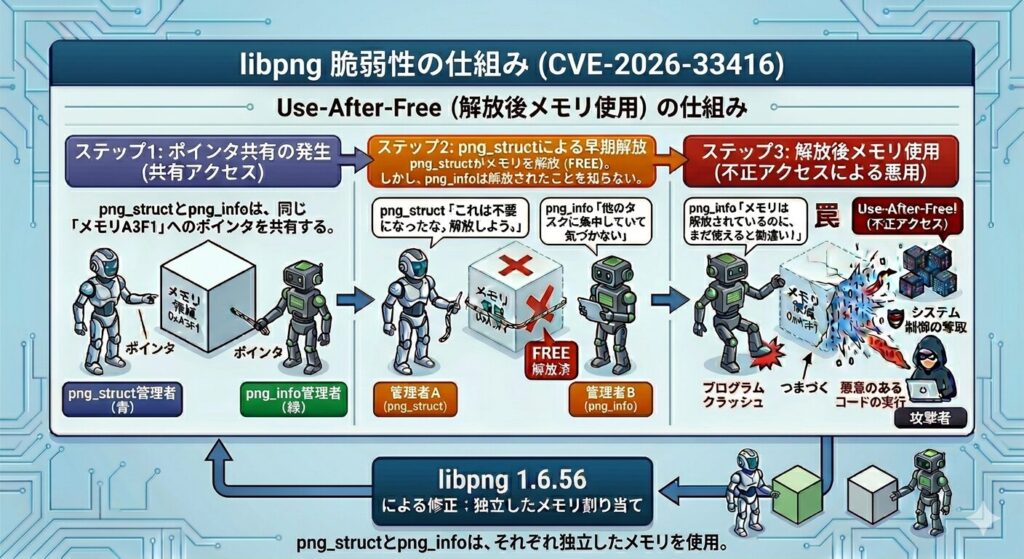
To briefly outline the attack flow, it goes as follows. Steps 3 through 6 correspond to the vulnerabilities discovered in libpng, and the diagram above illustrates how those vulnerabilities work.
1.The attacker creates a malicious PNG image
2.The image is uploaded to a website or system
3.libpng processes the image on the server side
4.A use-after-free vulnerability occurs
5.Memory corruption
6.Information disclosure or arbitrary code execution
In other words, attackers can carry out an attack by tricking users into uploading a malicious PNG image, and features that allow users to upload images, such as the one described below, serve as an entry point for the attack.
・Uploading profile pictures
・Attaching images to contact forms
・Generating thumbnails
・Sending images in chat
・Attaching images to emails
・AI image generation and analysis
・Surveillance camera image processing
・Medical imaging systems
From Vulnerability Discovery to Disclosure
Our engineers,
1.Discovery of vulnerabilities
2.Creation of Proof of Concept (PoC) code
3.Verification of attack feasibility
We carried out the necessary steps and reported the details of this vulnerability to the libpng maintainers.
Subsequently, a fix was developed in collaboration with the maintainers and developers, and the vulnerability was disclosed.
Our company conducts research and development in the following technical fields, and this vulnerability was discovered during these R&D activities.
・Efficient investigation and discovery of zero-day vulnerabilities
・Automation of penetration testing
・Security measures for the OT/IoT sector
・Investigation and research into advanced attack techniques that evade EDR and similar solutions
・Security measures leveraging large language models (LLMs)
About MUSHIKAGO and Our Initiatives
Our product, “MUSHIKAGO,” enables advanced security validation centered on automated penetration testing.
Our engineers, who possess the technical expertise to identify vulnerabilities, and our sales team, who sincerely address customer feedback and requests, work together as one to continue providing products and services that stay ahead of evolving cyberattacks and proactively implement countermeasures.
Reference
Archive
- April 2026
- March 2026
- November 2025
- October 2025
- September 2025
- June 2025
- March 2025
- February 2025
- October 2024
- August 2024
- May 2024
- April 2024
- March 2024
- February 2024
- November 2023
- October 2023
- April 2023
- September 2022
- August 2022
- July 2022
- June 2022
- April 2022
- March 2022
- December 2021
- October 2021
- August 2021