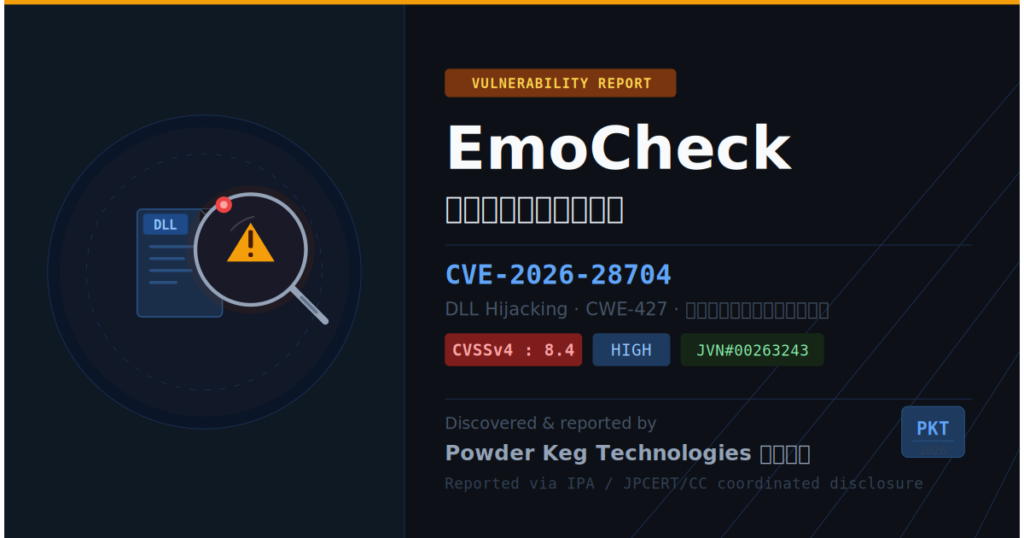
Our engineers have discovered a vulnerability (CVE-2026-28704) in JPCERT/CC’s “EmoCheck” tool!
Recently, one of our engineers discovered a vulnerability in “EmoCheck,” a tool provided by JPCERT/CC, a core cybersecurity organization in Japan. Following a report to the IPA, the vulnerability was officially published in JVN (Japan Vulnerability Notes).
In this article, we’ll provide a clear overview of this vulnerability, explain how we discovered it, and discuss what it means for corporate security measures.
EmoCheck の脆弱性(CVE-2026-28704)
Advisory: JVN#00263243
CVE: CVE-2026-28704
CVSSv3: 7.5
CVSSv4: 8.4
CWE: CWE-427(Uncontrolled Search Path Element)
Impact: High
Scope of Impact: EmoCheck All Versions
Attack Vector: An attack is possible if a malicious user distributes a tampered DLL (which must be placed in the same folder as EmoCheck)
What is EmoCheck?
EmoCheck is a tool developed and distributed free of charge by JPCERT/CC to easily check for infection by the highly destructive malware “Emotet.” Between 2019 and 2022, Emotet caused significant damage to companies and government agencies both in Japan and abroad, and many IT professionals made effective use of EmoCheck to prevent the spread of the infection.
Discovered Vulnerability: What Is “DLL Hijacking”?
The vulnerability discovered this time is a “DLL loading issue (CWE-427).”
Windows applications load specific “DLLs (library files)” when they start up in order to function. If there is an issue with the order in which DLLs are loaded from different folders, the application may unintentionally load a malicious DLL prepared by an attacker. This is known as “DLL hijacking.”
In the case of EmoCheck, the tool was designed such that simply placing a DLL with a specific name in the same folder as the tool would cause that DLL to be called when EmoCheck was executed.
A detailed description of the attack is clearly explained on JVN iPedia, so please refer to it.
Why were we able to discover this?
Through the development and operation of MUSHIKAGO, we are engaged in analyzing the behavior of malware and attack tools. This latest discovery also stemmed from an investigation conducted with the perspective of “Could widely used security tools themselves become attack vectors?”
Security products and tools provided by public institutions are often treated as “trustworthy.” However, precisely because of this, the damage caused when they are exploited by attackers can be significant. “Questioning what is trusted”—this is our research philosophy.
Following the discovery, we reported it in accordance with the standard responsible disclosure process through the Information Security Early Warning Partnership (IPA/JPCERT/CC), leading to this public disclosure.
What This Means: A Message to Corporate Security Professionals
This incident highlights one important point: even “security tools that were once used” can become targets of attack.
In corporate environments in particular, the following risks lurk:
- Temporarily downloaded tools remain on the system
- The old version of the software continues to run in the background
- We have not conducted an inventory of locations and devices that lack security personnel.
Today’s companies need a system that can identify these “hidden risks” and continuously monitor them.
How MUSHIKAGO Can Help You
Our hardware-based security testing device, “MUSHIKAGO,” is a tool designed to identify these hidden risks from the perspective of actual attacks.
- Quickly visualize devices within the organization
- Detect security risks for each device
- No internet connection required; also supports closed environments (factories, OT/ICS)
- Ministry of Economy, Trade and Industry (METI) Track Record of Designating Domestic Security Products
If your company is wondering, “Is our environment truly free of risks?” or “We’re considering penetration testing for the first time,” please feel free to contact us.
Click here for more information about MUSHIKAGO or to contact us
https://powderkegtech.com/ja/mushikago/
Reference
JVN#00263243 :https://jvn.jp/jp/JVN00263243/
JPCERT/CC Press Release:https://www.jpcert.or.jp/press/2026/PR20260410.html
JVN iPedia:https://jvndb.jvn.jp/ja/contents/2026/JVNDB-2026-000053.html
NIST:https://nvd.nist.gov/vuln/detail/CVE-2026-28704
Archive
- June 2026
- April 2026
- March 2026
- November 2025
- October 2025
- September 2025
- June 2025
- March 2025
- February 2025
- October 2024
- August 2024
- May 2024
- April 2024
- March 2024
- February 2024
- November 2023
- October 2023
- April 2023
- September 2022
- August 2022
- July 2022
- June 2022
- April 2022
- March 2022
- December 2021
- October 2021
- August 2021


