Penetration Testing Service
What is Penetration Testing?
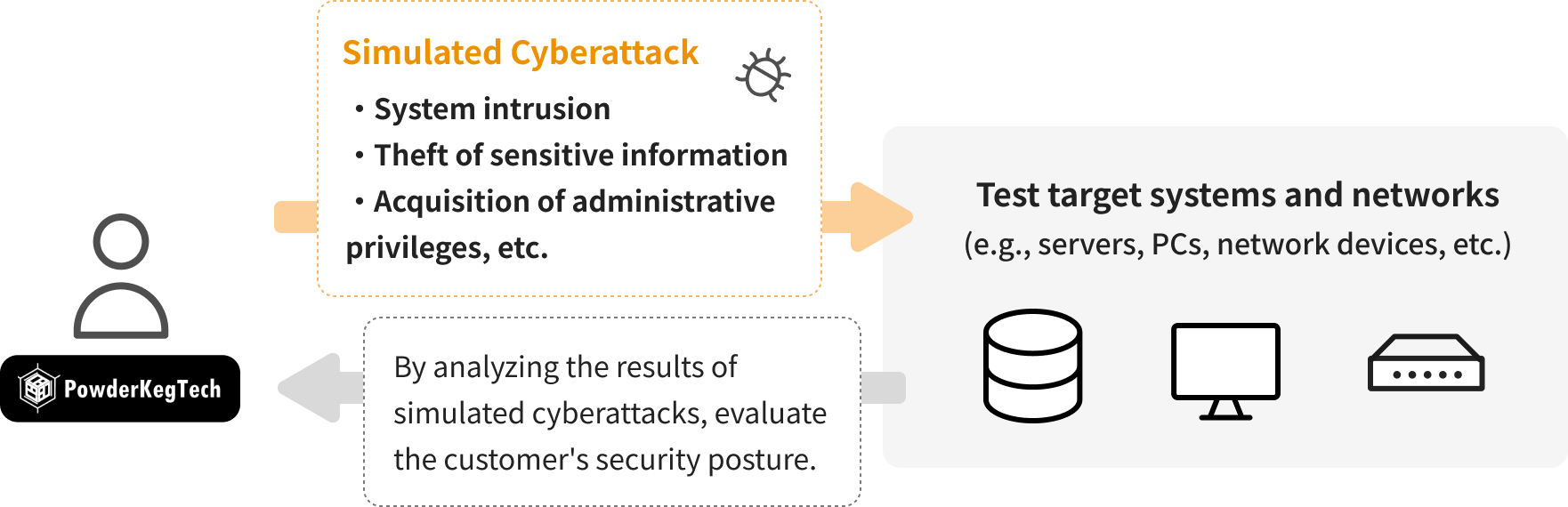
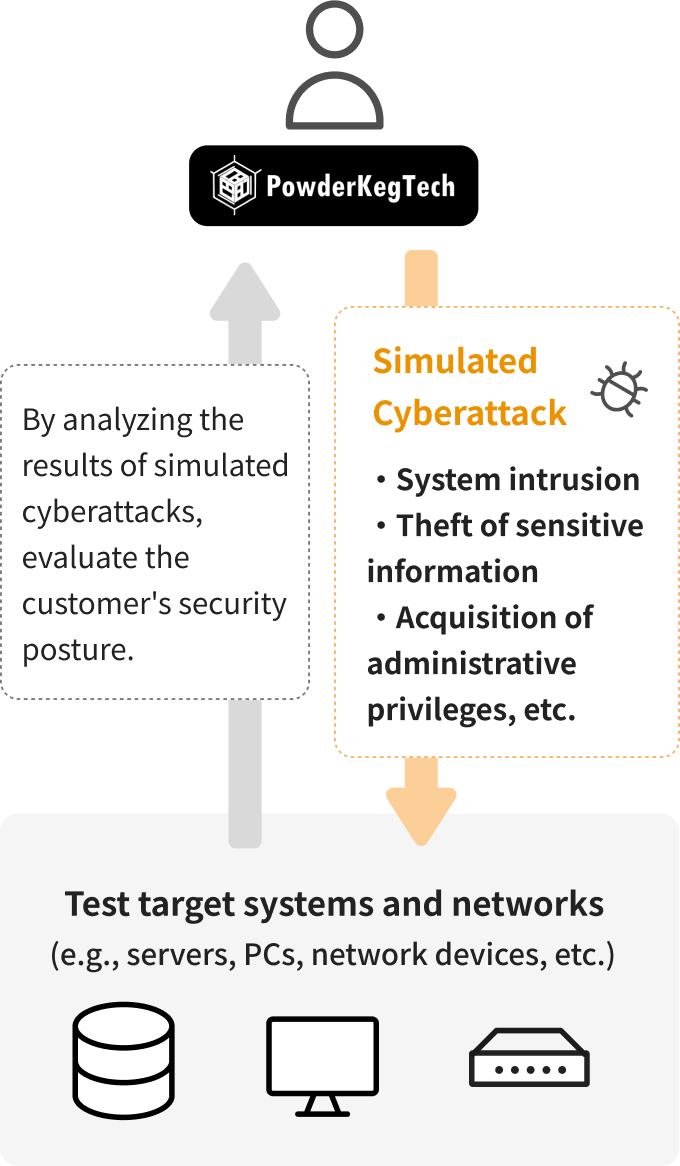
Penetration testing (also known as intrusion testing) is a service that evaluates the security of target systems or networks by simulating cyberattacks. The goal is to verify whether test objectives—such as system intrusion, theft of sensitive information, or acquisition of administrative privileges—can be achieved, and assess the effectiveness of the client’s security measures.
Many organizations regularly perform tabletop security risk assessments or incident response drills. However, few verify whether their security measures and response frameworks will function as expected during actual cyberattacks.
By utilizing our penetration testing services, clients can clearly understand the effectiveness of their internal security measures and frameworks.
Since the scope of systems, networks, scenarios, and reports varies significantly by client, we conduct thorough pre-testing consultations to tailor the service accordingly.
We offer optional re-testing services after the initial test. We believe it is crucial to verify whether identified security threats have been appropriately addressed.

Our penetration testing service is listed in the "Information Security Service Standards Compliant Service List" as a service that complies with the "Information Security Service Standards" established by the Ministry of Economy, Trade and Industry (METI) of Japan.
These standards were established by METI with the aim of identifying information security services that strive to maintain and improve a certain level of quality.
The compliance with these standards is confirmed through a review by the Japan Information Security Audit Association (JASA), a specified non-profit organization. It certifies that the service meets specific technical and quality management requirements, and demonstrates a commitment to maintaining and improving service quality.

Our Strengths in Penetration Testing Services
Comprehensive Testing through Manual and Automated Methods
・Penetration testing is often conducted within a limited timeframe. Our services leverage both manual testing by engineers and our proprietary automated penetration testing device, MUSHIKAGO, to perform as many tests as possible within the given timeframe and validate the client’s security risks.
Experienced Security Professionals
・Penetration testing experts certified by organizations like OffSec (e.g., OSCP), with experience in international Capture the Flag (CTF) competitions.
・Security experts with backgrounds in critical infrastructure organizations.
・Former consultants from major security firms providing customer-focused services.
・Developers of MUSHIKAGO, offering insights from a developer’s perspective.
Proven Record of Discovering New Vulnerabilities
・Our team includes members actively researching and investigating zero-day vulnerabilities. Depending on the scope of the test, we also examine specific vulnerabilities unique to the client’s environment.
Example Test Scenarios
Our service tailors the test content to the client’s specific needs. Here are examples of past test scenarios:

Test Methodology
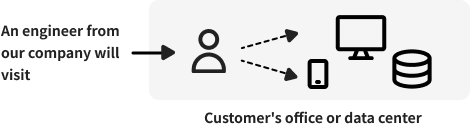
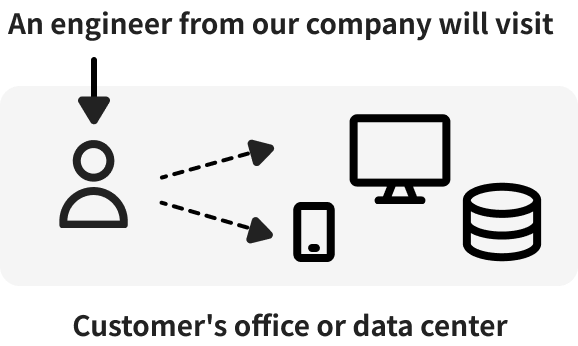
Clients can choose from the following two methods, or a hybrid approach, depending on their requirements:
Test Flow


Sample Test Items
Our test services are based on internationally recognized penetration testing standards such as NIST 800-115 and PTES (Penetration Testing Execution Standard). We also incorporate the latest security risks. Below are examples of remote test items for externally exposed systems:
Information Gathering on the Target Systems
| Test Item | Description |
| ICMP Scan | Utilize ICMP echo requests to confirm the existence of the target system. |
| TCP Scan | Conduct scans on TCP ports to identify open TCP ports on the target system. |
| UDP Scan | Conduct scans on UDP ports to identify open UDP ports on the target system. |
| OS and Version Detection | Analyze scan results to identify the operating system and its version on the target system. |
| Detection of Running Services and Version Identification | Analyze scan results to identify the exposed services and their respective versions. |
| FQDN and Domain Investigation | Investigate the Fully Qualified Domain Name (FQDN) and domain of the target system to confirm server and network information being used by the system. |
| Vulnerability Detection | Identify vulnerabilities based on the detected OS and service versions. Prioritize vulnerabilities that can be exploited for initial access or other purposes. |
| Exploration of Various Services | Test services like HTTP/HTTPS, SMB, SNMP, FTP, Telnet, SSH, RDP, and various databases by attempting logins using default credentials or password lists to confirm if credentials can be obtained. |
Initial Intrusion into Target System
| Test Item | Description |
| Remote Login Service Login Attempts | If services such as Telnet, SSH, RDP, or WinRM are available, use valid credentials to test login. |
| Exploit Code Execution | If publicly available exploit codes are applicable, execute them to establish reverse shells or test for arbitrary operations. |
Information Gathering Post-Initial Intrusion
| Test Item | Description |
| Search for Sensitive Information | Collect sensitive information such as account details stored within the system. |
| User Enumeration | Obtain a list of local users and, if applicable, Active Directory (AD) users. |
| Sensitive Information Search in AD Environments | Use techniques such as AS-REP Roasting, Kerberoasting, Silver/Golden Ticket, and DCsync to check if authentication information for AD users can be obtained. |
| Malware Protection Software Investigation | Obtain lists of running processes and files to verify the presence of endpoint protection platforms (EPP) or endpoint detection and response (EDR) solutions. |
| Local Vulnerability Scanning | Analyze patch information, installed packages, and program details to detect known vulnerabilities. Identify vulnerabilities that could be used for privilege escalation. |
| Sniffing and Communication Analysis | Capture communication data on the compromised device to identify the protocols used and analyze communication details. |
| Search for Usable Software | Identify software such as remote login tools or password managers that could be leveraged for privilege escalation or lateral movement. |
Privilege Escalation
| Test Item | Description |
| Using Vulnerabilities for Privilege Escalation | If vulnerabilities suitable for privilege escalation are detected during local vulnerability scans, test if escalation can be achieved using exploit codes. |
| Using Misconfigurations for Privilege Escalation | Test if processes running with administrative privileges can be edited or operated by standard users, or if commands executable by administrators can be run by standard users to escalate privileges. |
| Using Credentials for Privilege Escalation | Test if administrative credentials (passwords or hashes) obtained can be used for privilege escalation. |
Post-Privilege Escalation Information Gathering
| Test Item | Description |
| Search for Sensitive Information | Investigate the extended range of access granted by administrative privileges to confirm if sensitive information inaccessible to standard users can be obtained. |
| Search for Authentication Credentials | Access processes or memory storing authentication credentials to test if such credentials can be obtained. |
Lateral Movement to Other Systems
| Test Item | Description |
| Port Scanning on Other Devices | Conduct TCP/UDP port scans on other devices to identify services running on those systems. |
| Using Vulnerabilities for Lateral Movement | Exploit vulnerabilities on other devices to establish reverse shells or perform arbitrary operations. |
| Using Credentials for Lateral Movement | Use obtained credentials to attempt login to other systems. |
Report
The test results are presented in an easy-to-understand format for clients, utilizing frameworks such as MITRE ATT&CK. They also comply with international penetration testing standards, including NIST 800-115 and PTES (Penetration Testing Execution Standard).
The report primarily consists of the following sections:
1. Recommended Remediation Measures: Suggestions for addressing identified vulnerabilities.
2. Executive Summary: A concise overview of the test results.
3. Detailed Findings: A comprehensive summary of the test results.

Tools Used in this Test
In our testing service, we leverage the following tools, combining manual and automated testing methods to conduct assessments from all possible angles and perspectives:
Certifications and Expertise
Our engineers possess high skills and extensive experience, including certifications such as:
・Offsec Certifications (OSEP/OSCP,/OSWE etc.)
・PortSwigger Certifications (BSCP, etc.)
・Information Security Management Specialist
Pricing
We offer discounted rates when performing a platform assessment in addition to the web application assessment. For more details, please contact us.


Inquiries About the Service
Feel free to contact us with any questions about the service.